Hi @ZarkoGjurov,
Sorry for the slow delay to reply!
So I understand the need and desire behind this request, but I’m afraid I must deliver bad news. The short answer is no (sorry).
The medium answer is Tor Browser is a big piece of software and we don’t have the desire nor the capacity to add and maintain Windows 7 (or older!) support to an ever-growing set of dependencies. Even if it were possible for us get every dependency ‘working’ (with scare-quotes), we don’t have the ability to test or validate these changes, and keep on top of and back-porting security fixes for these dependencies.
The longer, more in-depth answer+justification follows:
First, let me give a simplified overview of what Tor Browser (on Desktop) is to set the stage for you.
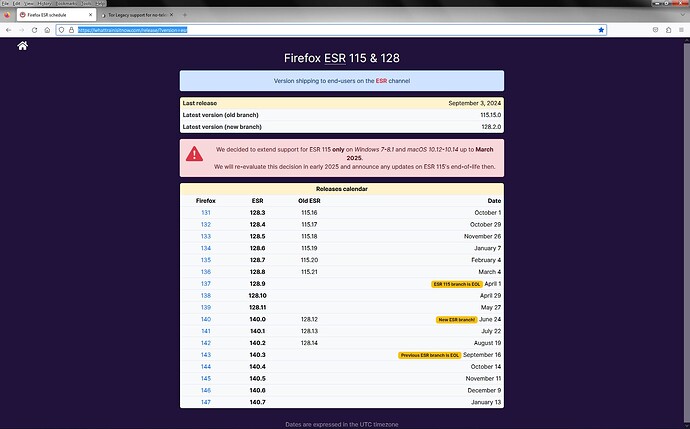
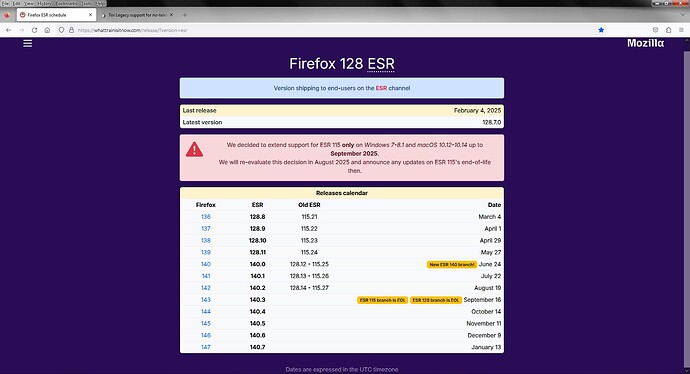
Tor Browser is a collection of about 100-ish (the actual number fluctuates between major releases, but this is the order of magnitude) patches sitting atop Firefox ESR (Extended Service Release, currently based off of Firefox 115 with monthly security backports). Our patchset improves various privacy and security properties of vanilla Firefox, backports some set of patches from Firefox RR (Rapid Release), adds some of our own customisations to the updater, integrates tor support for IP anonymity, adds some extra features around tor-specific functionality (circuit display, onion service auth, etc), and adds special logic for censorship circumvention.
Tor Browser also of course includes the tor daemon and its dependencies, and finally the pluggable transport binaries used by tor to circumvent censorship by obfuscating the tor network traffic in various ways.
Finally each of these 3 components are built reproducibly using the tor-browser-build system. This system ensures that the binaries we deliver to end users contain only the code we think they do by building everything ‘reproducibly’. Anyone on the internet can download our build system source, run our official build scripts, and get exactly the same output (after stripping code-signing signatures). This ensures that users don’t have to just trust us when it comes to our releases. Sometimes there are bugs in this system but they are given highest priority and block releases.
Each of these systems have problems when it comes to supporting older platforms:
Firefox
First of all, Firefox ESR does not maintain support for legacy systems. With Firefox 116 last summer, Mozilla dropped official support for Windows 7 and 8. This means they are now depending on (or at least not excluding) APIs only available in Windows 10 and on and we will inherit this change in Firefox ESR 128 this summer (Firefox ESR 115 is the last version of Firefox to support Windows 7). This will also have the cascading effect that Firefox’s dependencies will also no longer need to support these Windows versions, which means Mozilla will upgrade or add dependencies to libraries and functionality only available to newer Windows.
Historically, these changes and updates between versions (for instance, between the Windows Vista+ vs Windows 7+ min-spec boundary) has been in pretty important systems relating to browser security such as the process sand-boxing system. If we wanted to replace or stub out these systems to work on older Windows versions, the resulting product would necessarily be less secure on these systems. The work to maintain these legacy shims would only increase over-time as Mozilla’s dependencies stray further and further from Windows 7 compatibility.
Tor
The next problem we have is with the tor daemon on Windows. We’ve already encountered issues with Windows 7 versions of APIs being incompatible with modern tor (see: Non-fatal assertion now >= leg->link_sent_usec failed (#40830) · Issues · The Tor Project / Core / Tor · GitLab ). Fixing these issues have been either infeasible or not a high-priority for the network team given the relative lack of demand for Windows 7 support. This work would also likely fall onto the network team to make sure we don’t accidentally break things in the name of compatibility. We would expect this problem to continue to grow into the future.
Pluggable Transports
Our pluggable transports are small little programs which obfuscate tor’s network traffic to circumvent censorship which blocks vanilla tor. For historical reasons, these tools are built using the Go programming language which has a nice feature-set, but also a fairly aggressive update schedule. For instance, Go 1.21 dropped official support for Windows 7 earlier in the Tor Browser 13.0 release cycle (and indeed apps started breaking on Windows 7 around version 1.21.5). I forget the precise specifics off-hand, but basically we’ve had to hold back upgrading Go for some of our PTs on Windows, except for the ones which absolutely depend on the latest version’s features (Snowflake, if I recall correctly), to maintain support for existing Windows 7 installs. As a result, this particular PT does not work on Windows 7 and we simply don’t have the capacity to maintain a Go fork which works for older Windows.
The Build System
Just like any other software, compilers and build toolchains can have bugs and security issues that require us to update or else ship broken software to our users. The tor-browser-build build system used to build each of our Tor Browser releases is itself a bit of a behemoth and includes at the very least C/C++, Rust, Java, Kotlin, and Go build toolchains. If these tools are not maintaining compatibility with legacy operating system build targets then this back-compat work would also necessarily fall on us.
 Please Stop using Windows
Please Stop using Windows 
The browser team consists of myself and 6 engineers, supporting 3 desktop platforms and Android. If all the above problems were solvable (and also a good idea to solve), we don’t have the capacity or expertise to solve them on top of the existing maintenance workload. Keeping just the Firefox portion of Tor Browser running and up-to-date itself can be a challenging task.
Users of older operating systems (and really, Windows in general) should really migrate to Linux. Particularly, Tails ( https://tails.net/ ) is a great choice for those users which need Tor Browser and associated tools for whistle-blowing or censorship-circumvention use-cases. It’s even USB-bootable! Tor Browser also exist for Android as well!
Please upgrade.
best,
-richard