I read this announcement. Please revert the few patches. It is not a bug.
I believe the analysis behind removing this feature Mozilla included, is wrong.
In 2017 it was known Apple was going to start with on-device analyses.
There was never any question Apple was going to pull the stunts marketing-oriented companies were/are doing, sending your images and text to them for scrutiny, analysis, and retention; and then try to profit from it.
- 2021-06-07 TheVerge.com
Apple says the feature is enabled using “deep neural networks” and “on-device intelligence,” with the latter being the company’s preferred phrasing for machine learning. (It stresses Apple’s privacy-heavy approach to AI, which focuses on processing data on-device rather than sending it to the cloud.)
In the upcoming release of macOS 12 Monterey (as well as in iOS 15 and iPadOS 15), Safari automatically recognizes text in images on a web page and in the Photos app when you’re viewing an image. You can select and copy that text. The feature requires Apple’s neural engine, available in M1 Apple silicon Macs and mobiles with an A12 Bionic chip or later, which appeared starting in some iPhones in 2018 and some iPads in 2019. You can test this out using the public beta. It does an excellent job.
- 2021-09-29 CNBC.com
While object recognition has been around for a while, Apple says that its implementation differs because it happens on the device, instead of on a cloud server.
- 2021-09-21 9to5mac.com quoting Apple:
iOS 15 uses secure on-device intelligence
- Apple API Docs: Recognizing Text in Images
Add text-recognition features to your app using the Vision framework.
- Apple API Docs: Detecting Objects in Still Images
You can initialize a VNImageRequestHandler from image data in the following formats:
- Image data compressed or held in memory, as you might receive over a network connection. For example, photos downloaded from a website or the cloud fall into this category.
Emphasis mine.
Mozilla’s text recognition API is currently macOS only and calls out to these platfoms apis: Recognizing Text in Images | Apple Developer Documentation
In the future this could/should be replaced with local in-process OCR system like teseract ( https://github.com/tesseract-ocr/tesseract ). For now let’s neuter the global check to hard return false always and prevent all the dependent code paths from being taken.
I am not against open source but a bird in the hand is worth two in the bush. This is here now, not another large software project to ingest — after auditing it.
Under “Activity”
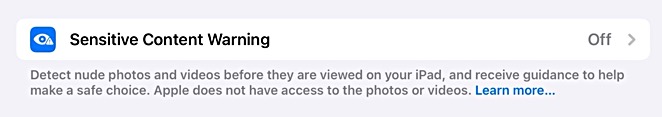
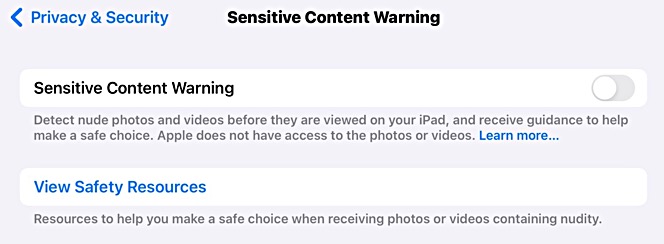
… we’re going to disable this (macOS-only) feature in Tor Browser because it calls out to macOS platform APIs with unknown local disk-leak defense or remote telemetry to Apple. Do you have a preference for Mullvad Browser?
As pointed out above, Apple performs this work on-device and in memory.
I read quite a few pages of Apple’s docs and see nothing even hinting they would write anything to disk versus point to the string in memory. It would be a waste of CPU, time, and battery power.
Where is the evidence anything is being written to disk, let alone sending anything to Apple.com?
Please revert this in this alpha. Thank you.