First, I looked up your username and that is pretty cool.
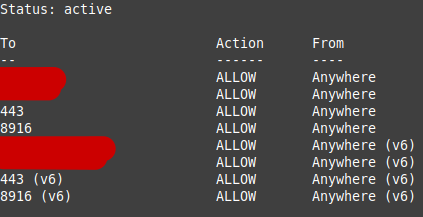
My DD-WRT does not have it’s firewall enabled but the computer that I plan to run the bridge on is a Ubuntu machine, which uses ufw.
Here is the output of sudo ufw status , if you are curious:
I changed ServerTransportListenAddr obfs4 0.0.0.0:443 to ServerTransportListenAddr obfs4 89.187.175.144:443.
I can see this being an issue in the future because I suppose that my public-facing IP stays constant… until I disable or change the active OpenVPN Client that is currently running on my DD-WRT router. I will use my current public IP to try to remedy the situation and go from there. Will take note of NoIP.
I attempted to replace PORT TO 8916 and PORT TO 443 with zeros or blanks and got this message:
“Port value is out of range [1-65535].”
Any ideas?
By “external IP address”, I assume that you mean public-facing IP address.
Will do! I replaced Address with Address 89.187.175.144
Here is my updated etc/tor/torrc file:
BridgeRelay 1
# Replace "TODO1" with a Tor port of your choice.
# This port must be externally reachable.
# Avoid port 9001 because it's commonly associated with Tor and censors may be scanning the Internet for this port.
# Note to self: Pulic IPv4 Address: 174.63.120.155
# Alternative public IP?: 127.0.1.1
Address 89.187.175.144
ORPort 8916 IPv4Only
AddressDisableIPv6 1
ServerTransportPlugin obfs4 exec /usr/bin/obfs4proxy
# Replace "TODO2" with an obfs4 port of your choice.
# This port must be externally reachable and must be different from the one specified for ORPort.
# Avoid port 9001 because it's commonly associated with Tor and censors may be scanning the Internet for this port.
# Robbie's backup port: 3818
ServerTransportListenAddr obfs4 89.187.175.144:443
# Local communication port between Tor and obfs4. Always set this to "auto".
# "Ext" means "extended", not "external". Don't try to set a specific port number, nor listen on 0.0.0.0.
ExtORPort auto
# Replace "<address@email.com>" with your email address so we can contact you if there are problems with your bridge.
# This is optional but encouraged.
ContactInfo <1rcummin@protonmail.com>
# Pick a nickname that you like for your bridge. This is optional.
Nickname macrohumanity
BandwidthRate 1 MBytes
I also removed PortForwarding 1 , which was suggested by saxon above.
Here is the latest journalctl -e -u tor@default output:
Sep 13 18:40:30 macrohumanity systemd[1]: Starting Anonymizing overlay network for TCP...
Sep 13 18:40:30 macrohumanity tor[942]: Sep 13 18:40:30.838 [notice] Tor 0.4.7.10 running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.2, Zlib 1.2.11, Liblzma 5.2.5, Libzstd 1.4.8 and Glibc 2.35 as libc.
Sep 13 18:40:30 macrohumanity tor[942]: Sep 13 18:40:30.838 [notice] Tor can't help you if you use it wrong! Learn how to be safe at https://support.torproject.org/faq/staying-anonymous/
Sep 13 18:40:30 macrohumanity tor[942]: Sep 13 18:40:30.839 [notice] Read configuration file "/usr/share/tor/tor-service-defaults-torrc".
Sep 13 18:40:30 macrohumanity tor[942]: Sep 13 18:40:30.839 [notice] Read configuration file "/etc/tor/torrc".
Sep 13 18:40:30 macrohumanity tor[942]: Sep 13 18:40:30.848 [notice] Based on detected system memory, MaxMemInQueues is set to 5769 MB. You can override this by setting MaxMemInQueues by hand.
Sep 13 18:40:30 macrohumanity tor[942]: Configuration was valid
Sep 13 18:40:30 macrohumanity tor[947]: Sep 13 18:40:30.999 [notice] Tor 0.4.7.10 running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.2, Zlib 1.2.11, Liblzma 5.2.5, Libzstd 1.4.8 and Glibc 2.35 as libc.
Sep 13 18:40:30 macrohumanity tor[947]: Sep 13 18:40:30.999 [notice] Tor can't help you if you use it wrong! Learn how to be safe at https://support.torproject.org/faq/staying-anonymous/
Sep 13 18:40:30 macrohumanity tor[947]: Sep 13 18:40:30.999 [notice] Read configuration file "/usr/share/tor/tor-service-defaults-torrc".
Sep 13 18:40:30 macrohumanity tor[947]: Sep 13 18:40:30.999 [notice] Read configuration file "/etc/tor/torrc".
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.018 [notice] Based on detected system memory, MaxMemInQueues is set to 5769 MB. You can override this by setting MaxMemInQueues by hand.
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Opening Socks listener on 127.0.0.1:9050
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Opened Socks listener connection (ready) on 127.0.0.1:9050
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Opening OR listener on 0.0.0.0:8916
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Opened OR listener connection (ready) on 0.0.0.0:8916
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Opening Extended OR listener on 127.0.0.1:0
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Extended OR listener listening on port 41117.
Sep 13 18:40:31 macrohumanity tor[947]: Sep 13 18:40:31.021 [notice] Opened Extended OR listener connection (ready) on 127.0.0.1:41117
Sep 13 18:40:31 macrohumanity Tor[947]: We compiled with OpenSSL 30000020: OpenSSL 3.0.2 15 Mar 2022 and we are running with OpenSSL 30000020: 3.0.2. These two versions should be binary compatible.
Sep 13 18:40:31 macrohumanity Tor[947]: Tor 0.4.7.10 running on Linux with Libevent 2.1.12-stable, OpenSSL 3.0.2, Zlib 1.2.11, Liblzma 5.2.5, Libzstd 1.4.8 and Glibc 2.35 as libc.
Sep 13 18:40:31 macrohumanity Tor[947]: Tor can't help you if you use it wrong! Learn how to be safe at https://support.torproject.org/faq/staying-anonymous/
Sep 13 18:40:31 macrohumanity Tor[947]: Read configuration file "/usr/share/tor/tor-service-defaults-torrc".
Sep 13 18:40:31 macrohumanity Tor[947]: Read configuration file "/etc/tor/torrc".
Sep 13 18:40:31 macrohumanity Tor[947]: Based on detected system memory, MaxMemInQueues is set to 5769 MB. You can override this by setting MaxMemInQueues by hand.
Sep 13 18:40:31 macrohumanity Tor[947]: Opening Socks listener on 127.0.0.1:9050
Sep 13 18:40:31 macrohumanity Tor[947]: Opened Socks listener connection (ready) on 127.0.0.1:9050
Sep 13 18:40:31 macrohumanity Tor[947]: Opening OR listener on 0.0.0.0:8916
Sep 13 18:40:31 macrohumanity Tor[947]: Opened OR listener connection (ready) on 0.0.0.0:8916
Sep 13 18:40:31 macrohumanity Tor[947]: Opening Extended OR listener on 127.0.0.1:0
Sep 13 18:40:31 macrohumanity Tor[947]: Extended OR listener listening on port 41117.
Sep 13 18:40:31 macrohumanity Tor[947]: Opened Extended OR listener connection (ready) on 127.0.0.1:41117
Sep 13 18:40:33 macrohumanity Tor[947]: Parsing GEOIP IPv4 file /usr/share/tor/geoip.
Sep 13 18:40:33 macrohumanity Tor[947]: Parsing GEOIP IPv6 file /usr/share/tor/geoip6.
Sep 13 18:40:33 macrohumanity Tor[947]: Configured to measure statistics. Look for the *-stats files that will first be written to the data directory in 24 hours from now.
Sep 13 18:40:35 macrohumanity Tor[947]: Your Tor server's identity key fingerprint is <private>
Sep 13 18:40:35 macrohumanity Tor[947]: Your Tor bridge's hashed identity key fingerprint is <private>
Sep 13 18:40:35 macrohumanity Tor[947]: Your Tor server's identity key <private> fingerprint is <private>
Sep 13 18:40:35 macrohumanity Tor[947]: You can check the status of your bridge relay at https://bridges.torproject.org/status?id=<private>
Sep 13 18:40:35 macrohumanity Tor[947]: Bootstrapped 0% (starting): Starting
Sep 13 18:40:36 macrohumanity Tor[947]: Starting with guard context "default"
Sep 13 18:40:57 macrohumanity Tor[947]: Signaled readiness to systemd
Sep 13 18:40:57 macrohumanity systemd[1]: Started Anonymizing overlay network for TCP.
Sep 13 18:40:57 macrohumanity Tor[947]: Server managed proxy encountered a method error. (obfs4 listen tcp 89.187.175.144:443: bind: cannot assign requested address)
Sep 13 18:40:57 macrohumanity Tor[947]: Managed proxy '/usr/bin/obfs4proxy' was spawned successfully, but it didn't launch any pluggable transport listeners!
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 5% (conn): Connecting to a relay
Sep 13 18:40:58 macrohumanity Tor[947]: Opening Socks listener on /run/tor/socks
Sep 13 18:40:58 macrohumanity Tor[947]: Opened Socks listener connection (ready) on /run/tor/socks
Sep 13 18:40:58 macrohumanity Tor[947]: Opening Control listener on /run/tor/control
Sep 13 18:40:58 macrohumanity Tor[947]: Opened Control listener connection (ready) on /run/tor/control
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 10% (conn_done): Connected to a relay
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 14% (handshake): Handshaking with a relay
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 15% (handshake_done): Handshake with a relay done
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 75% (enough_dirinfo): Loaded enough directory info to build circuits
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 90% (ap_handshake_done): Handshake finished with a relay to build circuits
Sep 13 18:40:58 macrohumanity Tor[947]: Bootstrapped 95% (circuit_create): Establishing a Tor circuit
Sep 13 18:41:00 macrohumanity Tor[947]: Bootstrapped 100% (done): Done
Sep 13 18:41:00 macrohumanity Tor[947]: Now checking whether IPv4 ORPort 89.187.175.144:8916 is reachable... (this may take up to 20 minutes -- look for log messages indicating success)
Sep 13 18:58:00 macrohumanity Tor[947]: Your network connection speed appears to have changed. Resetting timeout to 60000ms after 18 timeouts and 146 buildtimes.
Sep 13 19:00:58 macrohumanity Tor[947]: Your server has not managed to confirm reachability for its ORPort(s) at 89.187.175.144:8916. Relays do not publish descriptors until their ORPort and DirPort are reachable. Please check your firewalls, ports, address, /etc/hosts file, etc.