Sorry, I meant that it was getting blocked, and it appears that in some cases it works, in others it doesn’t. See this issue, and chat logs: 1, 2.
Yes, it is possible to set up your own broker and make proxies and the client use it, and you can configure your own STUN servers. See The Tor Project / Anti-censorship / Pluggable Transports / Snowflake · GitLab - there’s a README in each directory, you can configure that stuff with command line arguments. In the Tor Browser you check how the built-in Snowflake bridge line looks and modify it accordingly (“Add a bridge manually”). And you can set up a broker and a proxy on the same machine as well, if you want to.
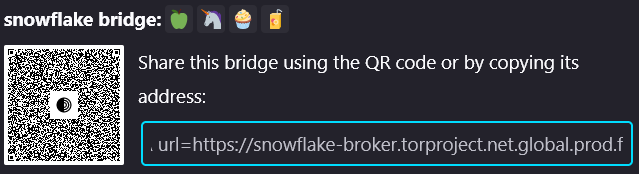
What I think would make more sense in case of the broker getting blocked (keep in mind that the connection to it is domain-fronted) is creating a proxy that lets you reach the broker, and modifying the client’s bridge line.
Here’s a discussion about alternative broker/signaling channels.
I haven’t heard of that, so I’ll let someone else answer it. This sounds strange.